Hacking J2ME on a Nokia phone...
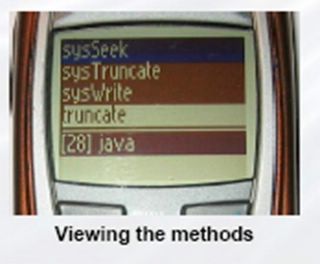
Adam Gowdiak has now shown us that J2ME can be hacked. He revealed this at last year's Hack in a Box conference (KL, Malaysia). The screenshot below is a MIDlet revealing method names in the underlying Java implementation - these are not public methods.
To quote from Adam's disclosure to the security community:
I verified on my Nokia DCT4 phone that malicious code exploiting one of the flaws can steal data from the phone (i.e. phonebook, SMS messages), establish communication with the Internet, send arbitrary SMS messages, write permanent memory of the phone (FLASH), interfere with or intercept IPC communication occurring between native Nokia OS tasks, install resident code on the phone. Any of the aforementioned actions can be conducted without user knowledge and permission.
Wow! That's NOT a small problem is it?
I downloaded Adam's presentation from the conference (watch out, it's 51 MBytes). It is a most fascinating read, if one can wade through the low-level programming exploits. I had to dig deep into my operating systems and assembly knowledge.
What impressed me was the systematic way that Adam went about first finding a way out of the Java sandbox, which is impressive enough. To then reverse engineer large parts of the underlying Nokia OS, that's indeed astonishing. It took him 4 months.
An initial reaction might be that this is an unusually resolute person going about an unusually arduous and difficult task. We shouldn't let that fool us. There are plenty of people out there with the knowledge and time to go about such a task. And, I can well imagine, it must be fun.
Anyone who's ever spent time in a lab with disassemblers and emulators trying to figure out a design, will know the kind of perverse satisfaction this can bring. Of course, it is not normal to spend so long crunching through code, but the lure of reaching the goal it unusually attractive.
I remember many years ago jumping with joy in a lab when I managed to make an LED light up by hacking into a processor board. Now, I had an hugely expensive HP 68030 emulator, one of only two in the world at the time. However, Adam was working "blind". He had to produce his own ARM "emulator" to run on the device and pipe out the data over the phone-to-PC wire.
Predictably, Sun played the vulnerability down. Astoundingly, they said it's not a problem because the MIDlet can just be deleted. Huh? I don't think they read Adam's presentation properly. (Actually, they probably did and it got them worried.)
We should not be in any doubt that mobile viruses will be a problem. This recent exploit should probably make handset vendors rethink how they implement their underlying operating systems to prevent reverse engineering. Also, encryption of key data on the device might also be worth considering.
The bottom line is that the problem should be fixed whilst it's still in its infancy.


0 Comments:
Post a Comment
<< Home